Instagram Brute Force CPU/GPU Supported 2024 (Use option 2 while running the script.) (Option 1 is on development) (Chrome should …


Instagram Brute Force CPU/GPU Supported 2024 (Use option 2 while running the script.) (Option 1 is on development) (Chrome should …
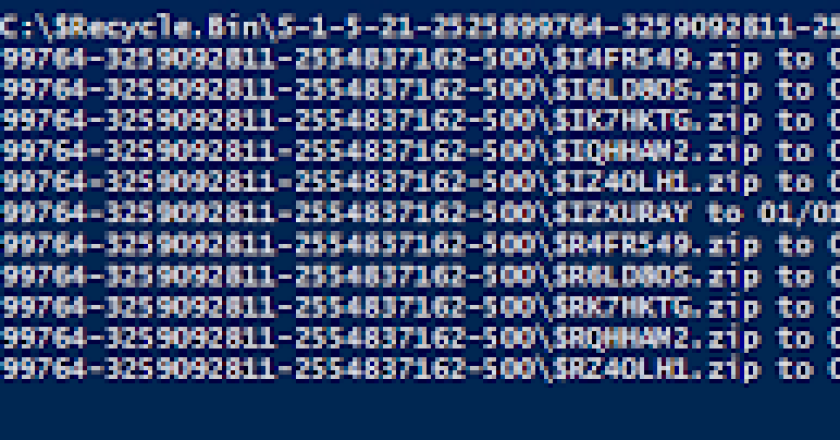
A PowerShell function to perform timestomping on specified files and directories. The function can modify timestamps recursively for all files …
Overview A bash script to retrieve user’s .plist files on a macOS system and to convert the data inside it …
A Cobalt Strike Beacon Object File (BOF) project which uses direct system calls to enumerate processes for specific modules or …
MacHound is an extension to the Bloodhound audting tool allowing collecting and ingesting of Active Directory relationships on MacOS hosts. …
Explore disassembly, binary exploitation & reverse-engineering through 10 little challenges. In the folder for each level you will find: flag …
Command-line tool to perform various persistence mechanism techniques on macOS. This tool was designed to be used by threat hunters …
Project iKy is a tool that collects information from an email and shows results in a nice visual interface. Visit …
PINEAPPLE MK7 REST CLIENT The leading rogue access point and WiFi pentest toolkit for close access operations. Passive and active …
Swiss Army Knife Proxy for rapid deployments. Supports multiple operations such as request/response dump, filtering and manipulation via DSL language, …