AzSubEnum is a specialized subdomain enumeration tool tailored for Azure services. This tool is designed to meticulously search and identify …
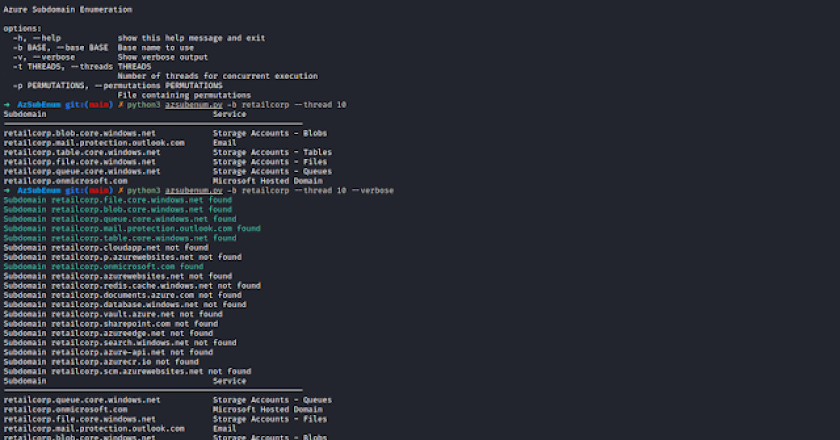
AzSubEnum is a specialized subdomain enumeration tool tailored for Azure services. This tool is designed to meticulously search and identify …

This repo contains the code for our USENIX Security ’23 paper “ARGUS: A Framework for Staged Static Taint Analysis of …
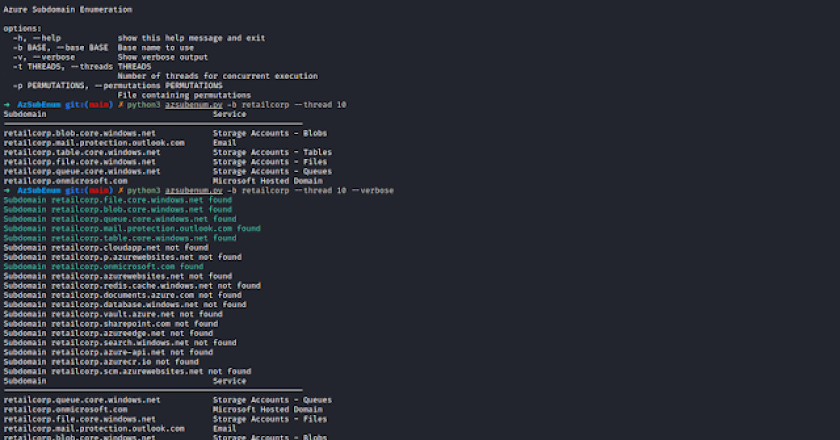
With the rapidly increasing variety of attack techniques and a simultaneous rise in the number of detection rules offered by …
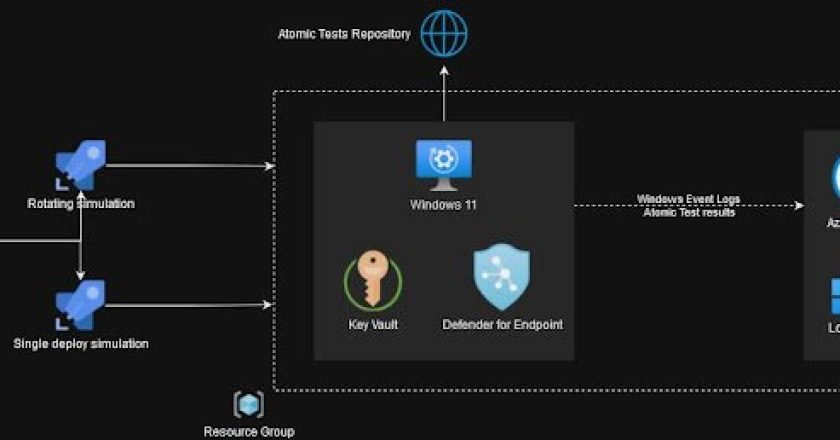
AntiSquat leverages AI techniques such as natural language processing (NLP), large language models (ChatGPT) and more to empower detection of …
Little AV/EDR Evasion Lab for training & learning purposes. (️ under construction..) ____ _ _____ ____ ____ ___ __ _____ …
Yet another tool – why? Existing tools don’t really “understand” code. Instead, they mostly parse texts. DeepSecrets expands classic regex-search …
Nodesub is a command-line tool for finding subdomains in bug bounty programs. It supports various subdomain enumeration techniques and provides …
What is it? Trawler is a PowerShell script designed to help Incident Responders discover potential indicators of compromise on Windows …
Upload_Bypass is a powerful tool designed to assist Pentesters and Bug Hunters in testing file upload mechanisms. It leverages various …
A DLL Loader With Advanced Evasive Features Features: CRT library independent. The final DLL file, can run the payload by …