One significant challenge to enjoying music while you swim is finding non-DRM MP3 files to load onto the internal storage …


One significant challenge to enjoying music while you swim is finding non-DRM MP3 files to load onto the internal storage …

If you read my coverage of smartwatches, then you’re likely familiar with past reviews of Mobvoi’s TicWatch models. The TicWatch …
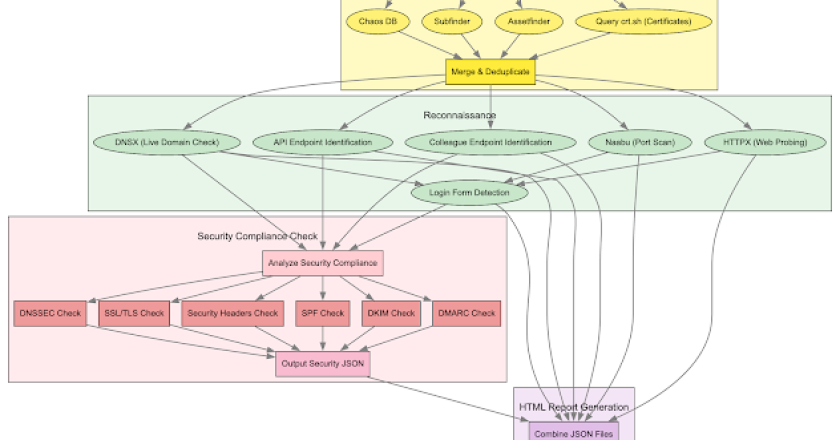
Frogy 2.0 is an automated external reconnaissance and Attack Surface Management (ASM) toolkit designed to map out an organization’s entire …

, and, boy, am I glad I did. They helped me get to sleep in minutes. For that reason, ZDNET …

If you want all the features of a smartwatch but can’t commit to a big, bulky watch face, you might …

PANO is a powerful OSINT investigation platform that combines graph visualization, timeline analysis, and AI-powered tools to help you uncover …

Amazon showcased its Fire TV Soundbar Plus Amazon Fire Soundbar Plus Chris Bayer/ZDNET Initially, I placed the two satellite speakers …

A Python script to check Next.js sites for corrupt middleware vulnerability (CVE-2025-29927). The corrupt middleware vulnerability allows an attacker to …

. Three connectors But there’s more: Unlike the USB-C breakaway connectors I’ve had previously, this one comes with three connectors: …

Bytes Revealer is a powerful reverse engineering and binary analysis tool designed for security researchers, forensic analysts, and developers. With …