Computer viruses are extremely hazardous, which is why it’s crucial to secure your devices with reliable malware removal programs. These …


Computer viruses are extremely hazardous, which is why it’s crucial to secure your devices with reliable malware removal programs. These …

This attack had all the hallmarks of ransomware attack and targeted CDK Global systems used by auto dealerships to manage …

Distributed denial-of-service attacks pose an increasing threat to organizations, with even some of the largest firms suffering significant disruptions from …
Criminal hackers employ ransomware attacks against their targets by encrypting their data and demanding that a ransom be paid within …
Cybersecurity refers to practices designed to defend computers, mobile devices, electronic data storage platforms and networks against attacks such as …
Malware refers to any form of malicious software which aims to disrupt, harm or steal private information for criminal use. …

iCloud can be an easy and secure way to back up photos and videos, but accessing those files across devices …

If the iPhone force restart does not work as intended, there may be an issue with the iOS system. To …
If the YouTube app on your iPhone is crashing or will not open, there are various fixes you can try, …
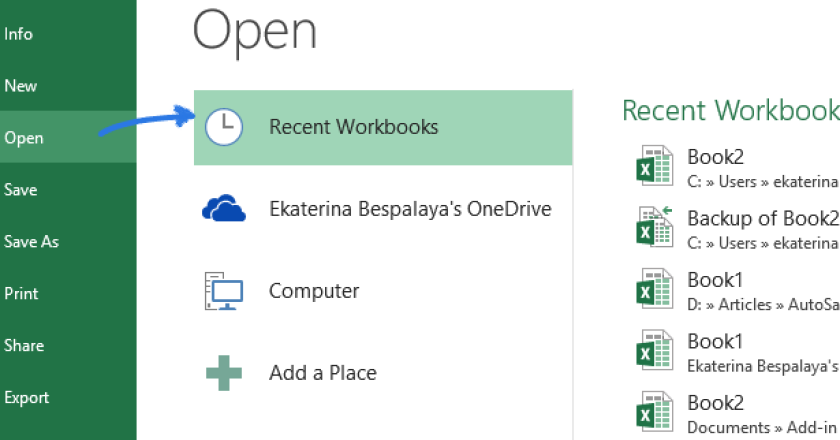
If your Excel file was left unsaved by accident, don’t fret – Microsoft understands mistakes happen and provides built-in functionality …