NoArgs is a tool designed to dynamically spoof and conceal process arguments while staying undetected. It achieves this by hooking …
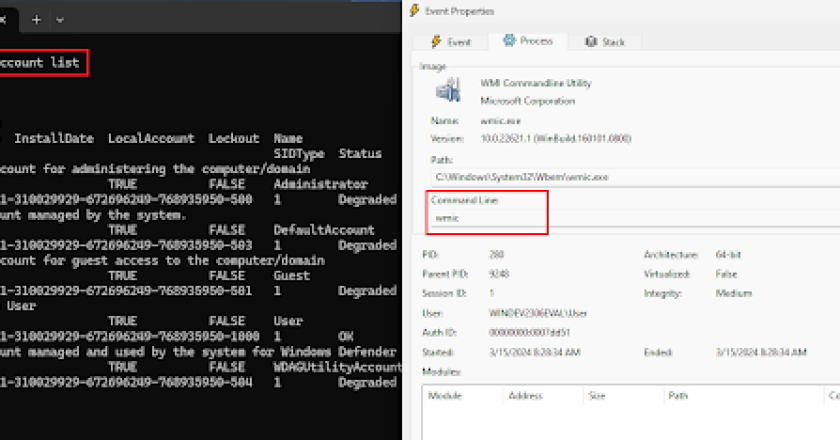
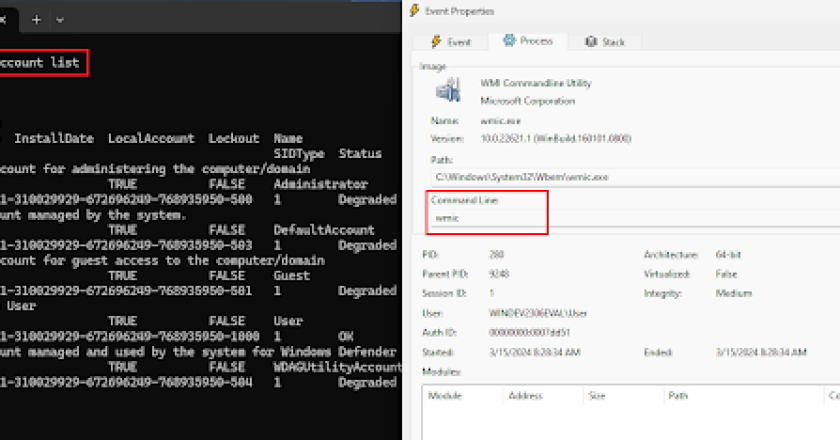
NoArgs is a tool designed to dynamically spoof and conceal process arguments while staying undetected. It achieves this by hooking …

Multi-cloud OSINT tool. Enumerate public resources in AWS, Azure, and Google Cloud. Currently enumerates the following: Amazon Web Services: – …
Microsoft ICS Forensics Tools is an open source forensic framework for analyzing Industrial PLC metadata and project files.it enables investigators …
Easy to use PowerShell script to enumerate access permissions in an Azure Active Directory environment. Background details can be found …
Reportly is an AzureAD user activity report tool. This is a tool that will help blue teams during a cloud …
ExchangeFinder is a simple and open-source tool that tries to find Micrsoft Exchange instance for a given domain based on …
AzureGraph is an Azure AD information gathering tool over Microsoft Graph. Thanks to Microsoft Graph technology, it is possible to …
SquarePhish is an advanced phishing tool that uses a technique combining the OAuth Device code authentication flow and QR codes. …
The BloodHound data collector for Microsoft Azure Get AzureHound Release Binaries Download the appropriate binary for your platform from one …
Welcome! This is a utility that can be compiled with Visual Studio 2019 (or newer). The goal of this program …