NativeDump allows to dump the lsass process using only NTAPIs generating a Minidump file with only the streams needed to …
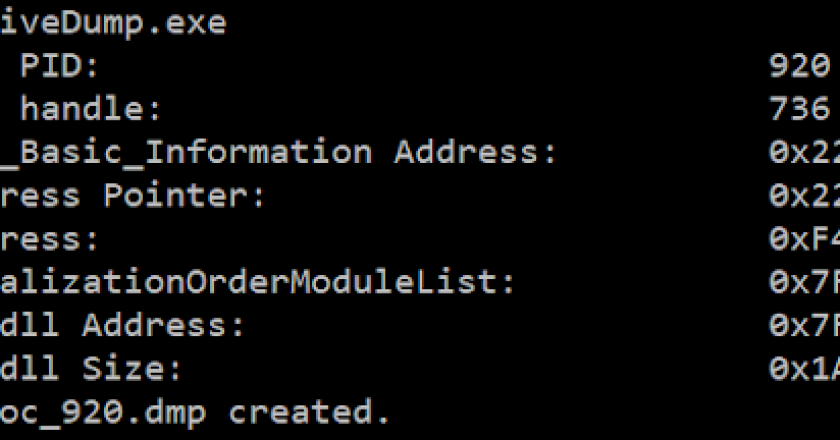
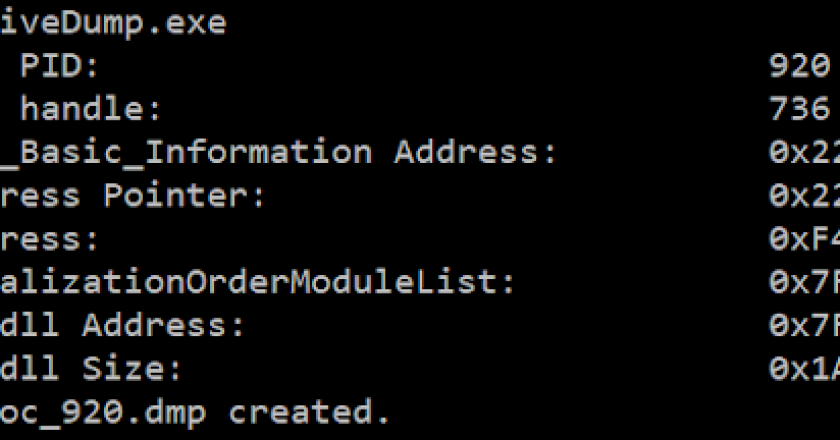
NativeDump allows to dump the lsass process using only NTAPIs generating a Minidump file with only the streams needed to …
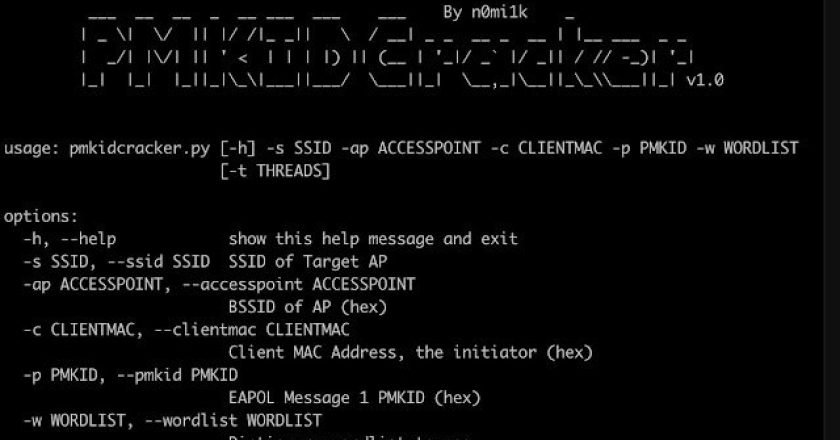
This program is a tool written in Python to recover the pre-shared key of a WPA2 WiFi network without any …
A GUI tool for viewing Windows Named Pipes and searching for insecure permissions. The tool was published as part of …
Double Venom (DVenom) is a tool that helps red teamers bypass AVs by providing an encryption wrapper and loader for …
GATOR – GCP Attack Toolkit for Offensive Research, a tool designed to aid in research and exploiting Google Cloud Environments. …
Commander is a command and control framework (C2) written in Python, Flask and SQLite. It comes with two agents written in …
ModuleShifting is stealthier variation of Module Stomping and Module overloading injection technique. It is actually implemented in Python ctypes so …
This POC is inspired by James Forshaw (@tiraniddo) shared at BlackHat USA 2022 titled “Taking Kerberos To The Next Level …
“Python memory module” AI generated pic – hotpot.ai pure-python implementation of MemoryModule technique to load a dll or unmanaged exe …
Villain is a Windows & Linux backdoor generator and multi-session handler that allows users to connect with sibling servers (other …