Pantheon is a GUI application that allows users to display information regarding network cameras in various countries as well as …
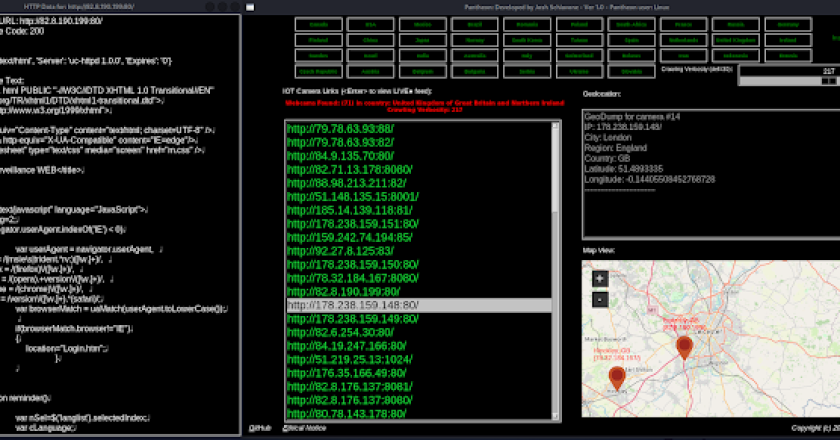
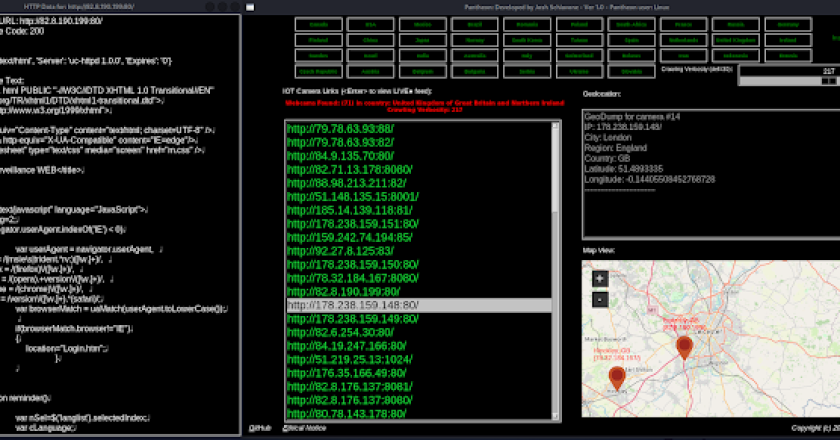
Pantheon is a GUI application that allows users to display information regarding network cameras in various countries as well as …
Reverse shell that can bypass windows defender detection $ apt install nim nim c -d:mingw –app:gui nimshell.nim Change the IP …
Description Welcome to the AD Pentesting Toolkit! This repository contains a collection of PowerShell scripts and commands that can be …
Anti Forensics Tool For Red Teamers, Used For Erasing Some Footprints In The Post Exploitation Phase. Reduces Payload Burnout And …
This is a powershell reverse shell that executes the commands and or scripts that you add to the powerreverse.ps1 file …
Introduction Another shellcode injection technique using C++ that attempts to bypass Windows Defender using XOR encryption sorcery and UUID strings …
With Microsoft’s recent announcement regarding the blocking of macros in documents originating from the internet (email AND web download), attackers …
In the age of EDR, red team operators cannot get away with using pre-compiled payloads anymore. As such, malware development …
Live Forensicator is part of the Black Widow Toolbox, its aim is to assist Forensic Investigators and Incidence responders in …
EDRHunt scans Windows services, drivers, processes, registry for installed EDRs (Endpoint Detection And Response). Read more about EDRHunt here. Install …