Free to use IOC feed for various tools/malware. It started out for just C2 tools but has morphed into tracking …
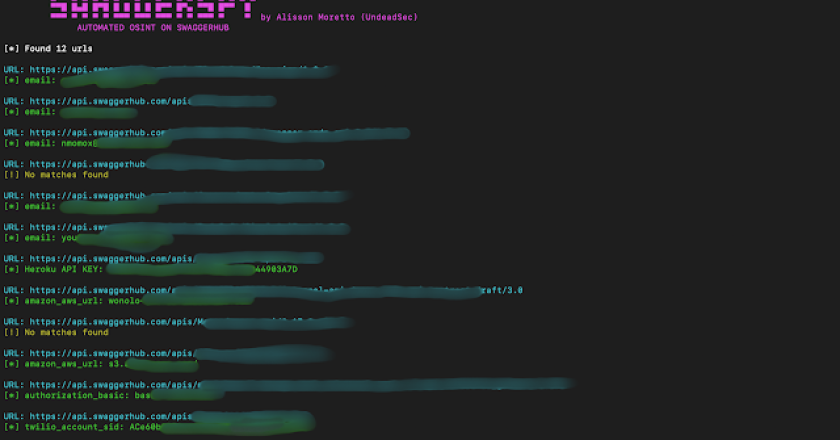
SwaggerSpy – Automated OSINT On SwaggerHub
SwaggerSpy is a tool designed for automated Open Source Intelligence (OSINT) on SwaggerHub. This project aims to streamline the process …

Melee – Tool To Detect Infections In MySQL Instances
MELEE: A Tool to Detect Ransomware Infections in MySQL Instances Attackers are abusing MySQL instances for conducting nefarious operations on …
Douglas-042 – Powershell Script To Help Speed Up Threat Hunting Incident Response Processes
DOUGLAS-042 stands as an ingenious embodiment of a PowerShell script meticulously designed to expedite the triage process and facilitate the …
HEDnsExtractor – Raw Html Extractor From Hurricane Electric Portal
Raw html extractor from Hurricane Electric portal Features Automatically identify IPAddr ou Networks through command line parameter or stdin Extract …
SOC-Multitool – A Powerful And User-Friendly Browser Extension That Streamlines Investigations For Security Professionals
Introducing SOC Multi-tool, a free and open-source browser extension that makes investigations faster and more efficient. Now available on the …
KoodousFinder – A Simple Tool To Allows Users To Search For And Analyze Android Apps For Potential Security Threats And Vulnerabilities
A simple tool to allows users to search for and analyze android apps for potential security threats and vulnerabilities Create …
Indicator-Intelligence – Finds Related Domains And IPv4 Addresses To Do Threat Intelligence After Indicator-Intelligence Collects Static Files
Finds related domains and IPv4 addresses to do threat intelligence after Indicator-Intelligence collects static files. Done Related domains, IPs collect …
X-force – IBM Security Utilitary Library In Python. Search And Query All Sources: Threat_Activities And Groups, Malware_Analysis, Industries
IBM Security X-FORCE Exchange library in Python 3. Search: threat_activities, threat_groups, malware_analysis, collector and industries. pip3 install XForce Using you API_KEY make …
EDRSandblast – Tool That Weaponize A Vulnerable Signed Driver To Bypass EDR Detections And LSASS Protections
EDRSandBlast is a tool written in C that weaponize a vulnerable signed driver to bypass EDR detections (Kernel callbacks and …
