A tool to find a company (target) infrastructure, files, and apps on the top cloud providers (Amazon, Google, Microsoft, DigitalOcean, …
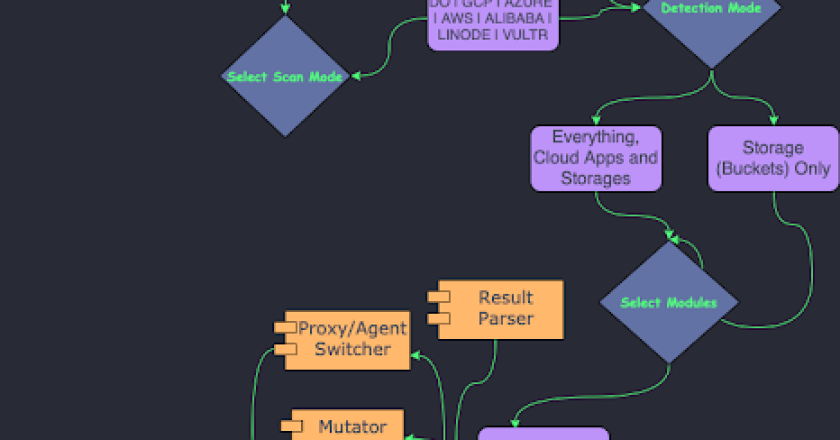
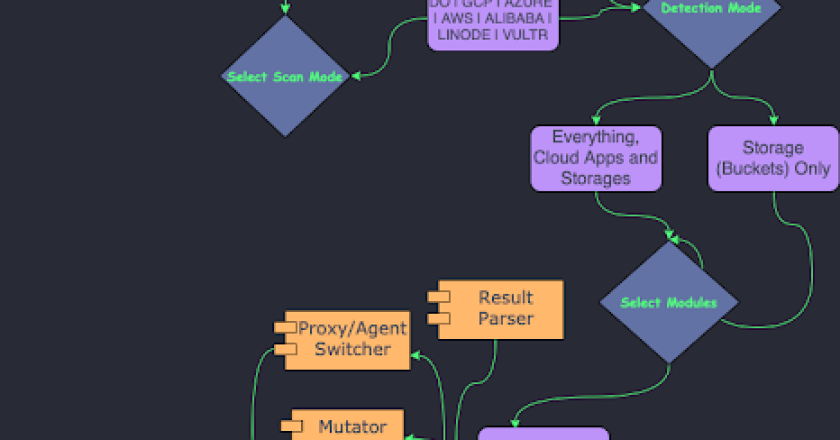
A tool to find a company (target) infrastructure, files, and apps on the top cloud providers (Amazon, Google, Microsoft, DigitalOcean, …

Shell command obfuscation to avoid SIEM/detection system During pentest, an important aspect is to be stealth. For this reason you …
Free to use IOC feed for various tools/malware. It started out for just C2 tools but has morphed into tracking …

This tool compilation is carefully crafted with the purpose of being useful both for the beginners and veterans from the …
Spoofy is a program that checks if a list of domains can be spoofed based on SPF and DMARC records. …
Escalate Service Account To LocalSystem via Kerberos. Friends familiar with the “Potato” series of privilege escalation should know that it …
During the reconnaissance phase, an attacker searches for any information about his target to create a profile that will later …
Documentation What is Bashfuscator? Bashfuscator is a modular and extendable Bash obfuscation framework written in Python 3. It provides numerous …
This tools is very helpful for finding vulnerabilities present in the Web Applications. A web application scanner explores a web …
Nidhogg is a multi-functional rootkit for red teams. The goal of Nidhogg is to provide an all-in-one and easy-to-use rootkit …