This post-exploitation keylogger will covertly exfiltrate keystrokes to a server. These tools excel at lightweight exfiltration and persistence, properties which …
This post-exploitation keylogger will covertly exfiltrate keystrokes to a server. These tools excel at lightweight exfiltration and persistence, properties which …
MultiDump is a post-exploitation tool written in C for dumping and extracting LSASS memory discreetly, without triggering Defender alerts, with …
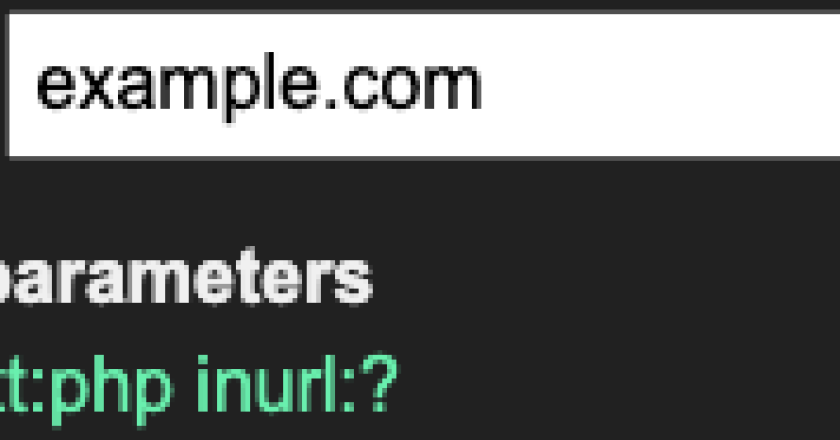
This is an evolution of the original getAllParams extension for Burp. Not only does it find more potential parameters for …
Shodan Dorks by twitter.com/lothos612 Feel free to make suggestions city: Find devices in a particular city. city:”Bangalore” country: Find devices …

mapXplore is a modular application that imports data extracted of the sqlmap to PostgreSQL or SQLite database. Its main features …
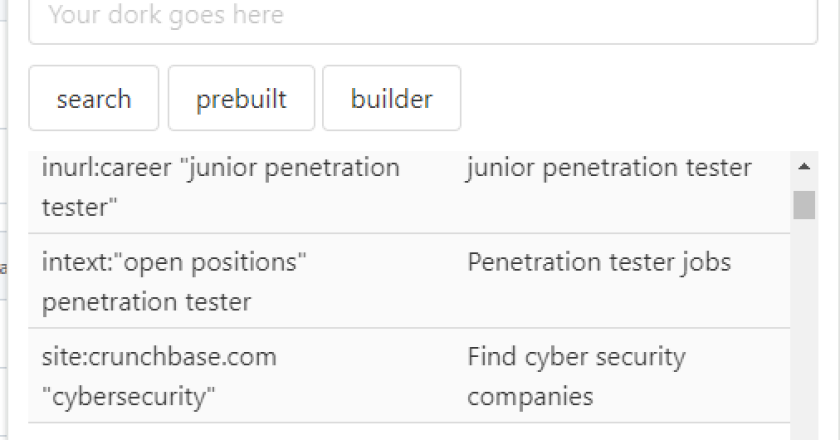
During reconaissance phase or when doing OSINT , we often use google dorking and shodan and thus the idea of …
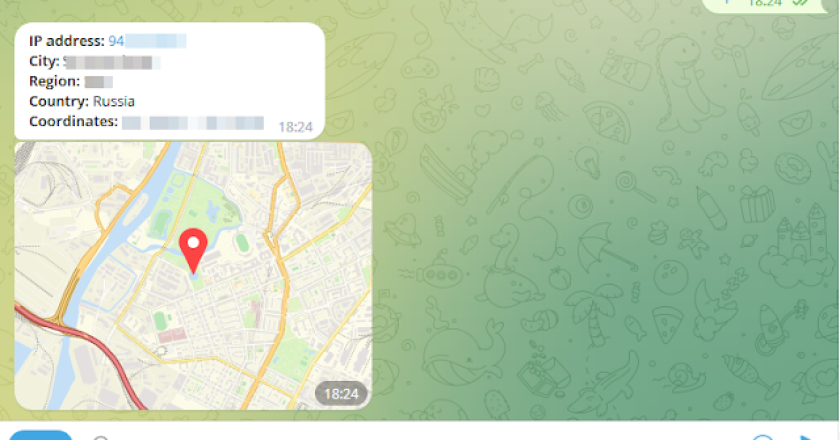
Remote administration crossplatfrom tool via telegram\ Coded with ❤️ python3 + aiogram3\ https://t.me/pt_soft v0.3 [X] Screenshot from target [X] Crossplatform …
A list of Google Dorks for Bug Bounty, Web Application Security, and Pentesting Live Tool Broad domain search w/ negative …

GTFOcli it’s a Command Line Interface for easy binaries search commands that can be used to bypass local security restrictions …

nomore403 is an innovative tool designed to help cybersecurity professionals and enthusiasts bypass HTTP 40X errors encountered during web security …