A tool to find a company (target) infrastructure, files, and apps on the top cloud providers (Amazon, Google, Microsoft, DigitalOcean, …
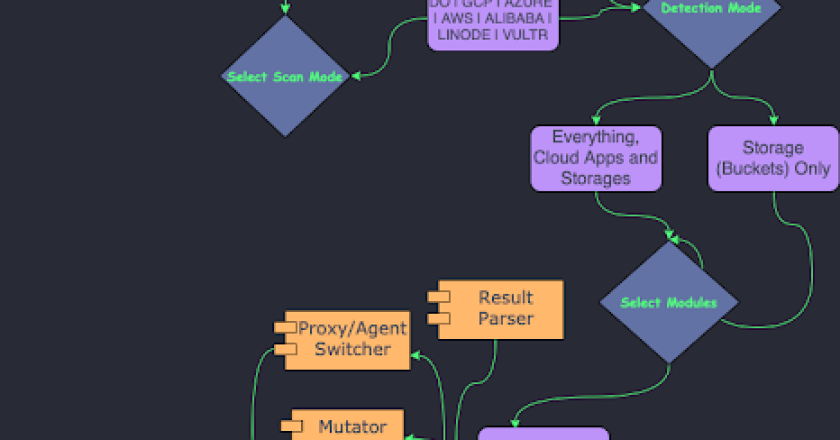
A tool to find a company (target) infrastructure, files, and apps on the top cloud providers (Amazon, Google, Microsoft, DigitalOcean, …

Tool for Fingerprinting HTTP requests of malware. Based on Tshark and written in Python3. Working prototype stage 🙂 Its main …

A vulnerable application made using node.js, express server and ejs template engine. This application is meant for educational purposes only. …

XM Goat is composed of XM Cyber terraform templates that help you learn about common Azure security issues. Each template …
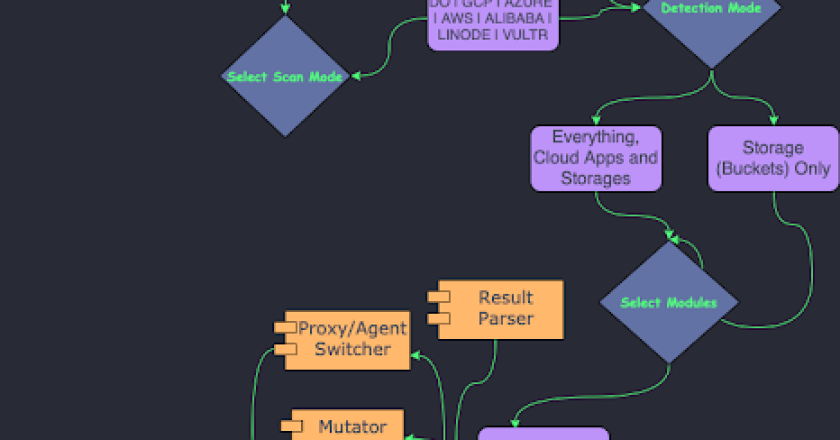
Analyse binaries for missing security features, information disclosure and more. Extrude is in the early stages of development, and currently …

A proof-of-concept User-Defined Reflective Loader (UDRL) which aims to recreate, integrate, and enhance Cobalt Strike’s evasion features! Contributors: UDRL Usage …

Shell command obfuscation to avoid SIEM/detection system During pentest, an important aspect is to be stealth. For this reason you …

CyberChef is a simple, intuitive web app for carrying out all manner of “cyber” operations within a web browser. These …
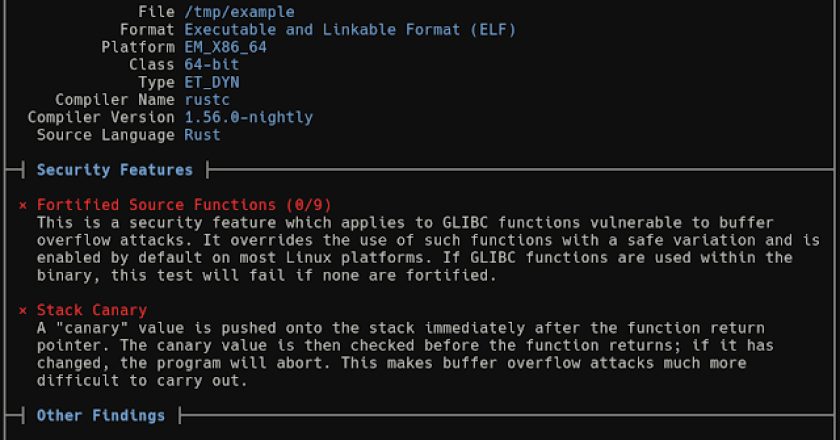
NativeDump allows to dump the lsass process using only NTAPIs generating a Minidump file with only the streams needed to …

Pyrit allows you to create massive databases of pre-computed WPA/WPA2-PSK authentication phase in a space-time-tradeoff. By using the computational power …