APIs For OSINT This is a Collection of APIs that will be useful for automating various tasks in OSINT. Thank …


APIs For OSINT This is a Collection of APIs that will be useful for automating various tasks in OSINT. Thank …

PANO is a powerful OSINT investigation platform that combines graph visualization, timeline analysis, and AI-powered tools to help you uncover …
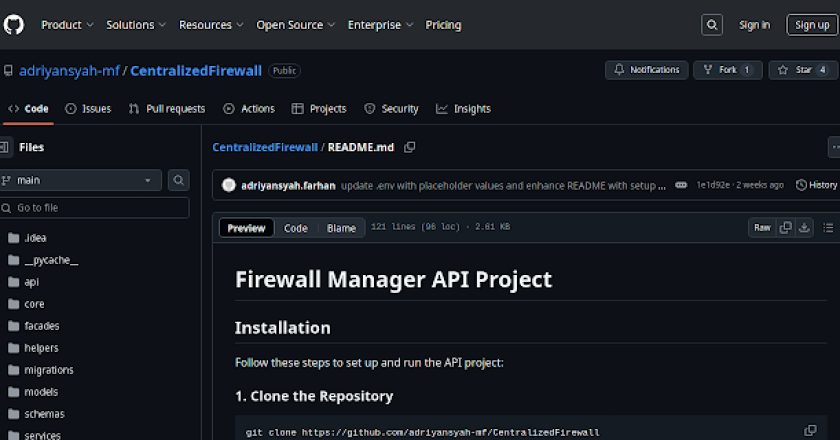
Installation Follow these steps to set up and run the API project: 1. Clone the Repository git clone https://github.com/adriyansyah-mf/CentralizedFirewallcd CentralizedFirewall …
secator is a task and workflow runner used for security assessments. It supports dozens of well-known security tools and it …

JA4+ is a suite of network Fingerprinting methods that are easy to use and easy to share. These methods are both …

Espionage is a network packet sniffer that intercepts large amounts of data being passed through an interface. The tool allows …
Free to use IOC feed for various tools/malware. It started out for just C2 tools but has morphed into tracking …

About skytrack is a command-line based plane spotting and aircraft OSINT reconnaissance tool made using Python. It can gather aircraft information …
This post-exploitation keylogger will covertly exfiltrate keystrokes to a server. These tools excel at lightweight exfiltration and persistence, properties which …

This is a tool designed for Open Source Intelligence (OSINT) purposes, which helps to gather information about employees of a …